This PR introduces volume encryption option to service offerings and disk offerings. Fixes #136 There is a hypervisor component and a storage pool component. Hypervisors are responsible for being capable of running/using the encrypted volumes. Storage pools are responsible for being able to create, copy, resize, etc. Hypervisors will report encryption support in their details, storage pools are marked for encryption support by pool type. The initial offering for experimental release of this feature will have support for encryption on Local, NFS, SharedMountPoint, and ScaleIO storage types. When volumes choosing an encrypted offering are allocated to a pool, the pool type must be capable of supporting encryption and this is enforced. When VMs are started and they have an encrypted volume, the hypervisor must be capable of supporting encryption. Also, if volumes are attached to running VMs, the attach will only work if the hypervisor supports encryption. This change includes a few other minor changes - for example the ability to force the KVM hypervisor private IP. This was necessary in my testing of ScaleIO, where the KVM hypervisors had multiple IPs and the ScaleIO storage only functions if the hypervisor as a ScaleIO client matches IPs with what CloudStack sees as the hypervisor IP. For experimental release of this feature, some volume workflows like extract volume and migrate volume aren't supported for encrypted volumes. In the future we could support these, as well as migrating from unencrypted to encrypted offerings, and vice versa. It may also be possible to configure encryption specifics in the future, perhaps at the pool level or the offering level. Currently, there is only one workable encryption offering for KVM that is supported by Libvirt and Qemu for raw and qcow2 disk files, LUKS version 1. This PR ensures we at least store this encryption format associated with each volume, with the expectation that later we may have LUKS v2 volumes or something else. Thus we will have the information necessary to use each volume with Libvirt if/when other formats are introduced. I think the most disruptive change here is probably a refactoring of the QemuImg utility to support newer flags like --object. I've tested the change against the basic Qemu 1.5.3 that comes with EL7 and I believe it is good, but it will be nice to see the results of some functional tests. Most of the other changes are limited to changing behavior only if volume encryption is requested. Working on documentation for the CloudStack docs. One thing to note is that hypervisors that run the stock EL7 version of Qemu will not support encryption. This is tested to be detected and report properly via the CloudStack API/UI. I intend to like to have a support matrix in the CloudStack docs. I may add a few more unit tests. I'd also like some guidance on having functional tests. I'm not sure if there's a separate framework, or if Marvin is still used, or what the current thing is. * Add Qemu object flag to QemuImg create * Add apache license header to new files * Add Qemu object flag to QemuImg convert * Set host details if hypervisor supports LUKS * Add disk encrypt flag to APIs, diskoffering * Schema upgrade 4.16.0.0 to 4.16.1.0 to support vol encryption * Add Libvirt secret on disk attach, and refer to it in disk XML * Add implementation of luks volume encryption to QCOW2 and RAW disk prep * Start VMs that have encrypted volumes * Add encrypt option to service offering and root volume provisioning * Refactor volume passphrase into its own table and object * CryptSetup, use key files to pass keys instead of command line * Update storage types and allocators to select encryption support * Allow agent.properties to define the hypervisor's private IP * Implement createPhysicalDisk for ScaleIOStorageAdaptor * UI: Add encrypt options to offerings * UI module security updates * Revert "UI module security updates" - belongs in base This reverts commit a7cb7cf7f57aad38f0b5e5d67389c187b88ffd94. * Add --target-is-zero support for QemuImg * Allow qemu image options to be passed, API support convert encrypted * Switch hypervisor encryption support detection to use KeyFiles * Fixes for ScaleIO root disk encryption * Resize root disk if it won't fit encryption header * Use cryptsetup to prep raw root disks, when supported * Create qcow2 formatting if necessary during initial template copy to ScaleIO * Allow setting no cache for qemu-img during disk convert * Use 1M sparse on qemu-img convert for zero target disks * UI: Add volume encryption support to hypervisor details * QemuImg use --image-opts and --object depending on version * Only send storage commands that require encryption to hosts that support encryption * Move host encryption detail to a static constant * Update host selection to account for volume encryption support Only attach volumes if encryption requirements are met * Ensure resizeVolume won't allow changing encryption * Catch edge cases for clearing passphrase when volume is removed * Disable volume migration and extraction for encrypted volumes * Register volume secret on destination host during live migration * Fix configdrive path editing during live migration * Ensure configdrive path is edited properly during live migration * Pass along and store volume encryption format during creation * Fixes for rebase * Fix tests after rebase * Add unit tests for DeploymentPlanningManagerImpl to support encryption * Deployment planner tests for encryption support on last host * Add deployment tests for encryption when calling planner * Added Libvirt DiskDef test for encryption details * Add test for KeyFile utility * Add CryptSetup tests * Add QemuImageOptionsTest * add smoke tests for API level changes on create/list offerings * Fix schema upgrade, do disk_offering_view first * Fix UI to show hypervisor encryption support * Load details into hostVO before trying to query them for encryption * Remove whitespace in CreateNetworkOfferingTest * Move QemuImageOptions to use constants for flag keys * Set physical disk encrypt format during createDiskFromTemplate in KVM Agent * Whitespace in AbstractStoragePoolAllocator * Fix whitespace in VolumeDaoImpl * Support old Qemu in convert * Log how long it takes to generate a passphrase during volume creation * Move passphrase generation to async portion of createVolume * Revert "Allow agent.properties to define the hypervisor's private IP" This reverts commit 6ea9377505f0e5ff9839156771a241aaa1925e70. * Updated ScaleIO/PowerFlex storage plugin to support separate (storage) network for Host(KVM) SDC connection. (#144) * Added smoke tests for volume encryption (in KVM). (#149) * Updated ScaleIO pool unit tests. * Some improvements/fixes for code smells (in ScaleIO storage plugin). * Updated review changes for ScaleIO improvements. * Updated host response parameter 'encryptionsupported' in the UI. * Move passphrase generation for the volume to async portion, while deploying VM (#158) * Move passphrase generation for the volume to async portion, while deploying VM. * Updated logs, to include volume details. * Fix schema upgrade, create passphrase table first * Fixed the DB upgrade issue (as noticed in the logs below.) DEBUG [c.c.u.d.ScriptRunner] (main:null) (logid:) CALL `cloud`.`IDEMPOTENT_ADD_FOREIGN_KEY`('cloud.volumes', 'passphrase', 'id') ERROR [c.c.u.d.ScriptRunner] (main:null) (logid:) Error executing: CALL `cloud`.`IDEMPOTENT_ADD_FOREIGN_KEY`('cloud.volumes', 'passphrase', 'id') ERROR [c.c.u.d.ScriptRunner] (main:null) (logid:) java.sql.SQLException: Failed to open the referenced table 'passphrase' ERROR [c.c.u.DatabaseUpgradeChecker] (main:null) (logid:) Unable to execute upgrade script * Fixes for snapshots with encrypted qcow2 Fixes #159 #160 #163 * Support create/delete encrypted snapshots of encrypted qcow2 volumes * Select endpoints that support encryption when snapshotting encrypted volumes * Update revert snapshot to be compatible with encrypted snapshots * Disallow volume and template create from encrypted vols/snapshots * Disallow VM memory snapshots on encrypted vols. Fixes #157 * Fix for TemplateManagerImpl unit test failure * Support offline resize of encrypted volumes. Fixes #168 * Fix for resize volume unit tests * Updated libvirt resize volume unit tests * Support volume encryption on kvm only, and passphrase generation refactor (#169) * Fail deploy VM when ROOT/DATA volume's offering has encryption enabled, on non-KVM hypervisors * Fail attach volume when volume's offering has encryption enabled, on non-KVM hypervisors * Refactor passphrase generation for volume * Apply encryption to dest volume for live local storage migration fixes #161 * Apply encryption to data volumes during live storage migration Fixes #161 * Use the same encryption passphrase id for migrating volumes * Pass secret consumer during storage migration prepare Fix for #161 * Fixes create / delete volume snapshot issue, for stopped VMs * Block volume snapshot if encrypted and VM is running Fixes #159 * Block snap schedules on encrypted volumes Fix for #159 * Support cryptsetup where luks type defaults to 2 Fixes #170 * Modify domain XML secret UUID when storage migrating VM Fix for #172 * Remove any libvirt secrets on VM stop and post migration Fix for #172 * Update disk profile with encryption requirement from the disk offering (#176) Update disk profile with encryption requirement from the disk offering and some code improvements * Updated review changes / javadoc in ScaleIOUtil Co-authored-by: Marcus Sorensen <mls@apple.com> Co-authored-by: Suresh Kumar Anaparti <sureshkumar.anaparti@gmail.com> Co-authored-by: Suresh Kumar Anaparti <suresh.anaparti@shapeblue.com> |
||
|---|---|---|
| .. | ||
| docs | ||
| nginx | ||
| public | ||
| src | ||
| tests | ||
| .babelrc | ||
| .editorconfig | ||
| .env.local.example | ||
| .env.local.https.example | ||
| .env.primate-qa | ||
| .gitattributes | ||
| .gitignore | ||
| .prettierrc | ||
| Dockerfile | ||
| LICENSE | ||
| README.md | ||
| babel.config.js | ||
| docker.sh | ||
| index.html | ||
| jest.config.js | ||
| jsconfig.json | ||
| package-lock.json | ||
| package.json | ||
| postbuild.sh | ||
| prebuild.sh | ||
| theme.config.js | ||
| vue.config.js | ||
| webstorm.config.js | ||
README.md
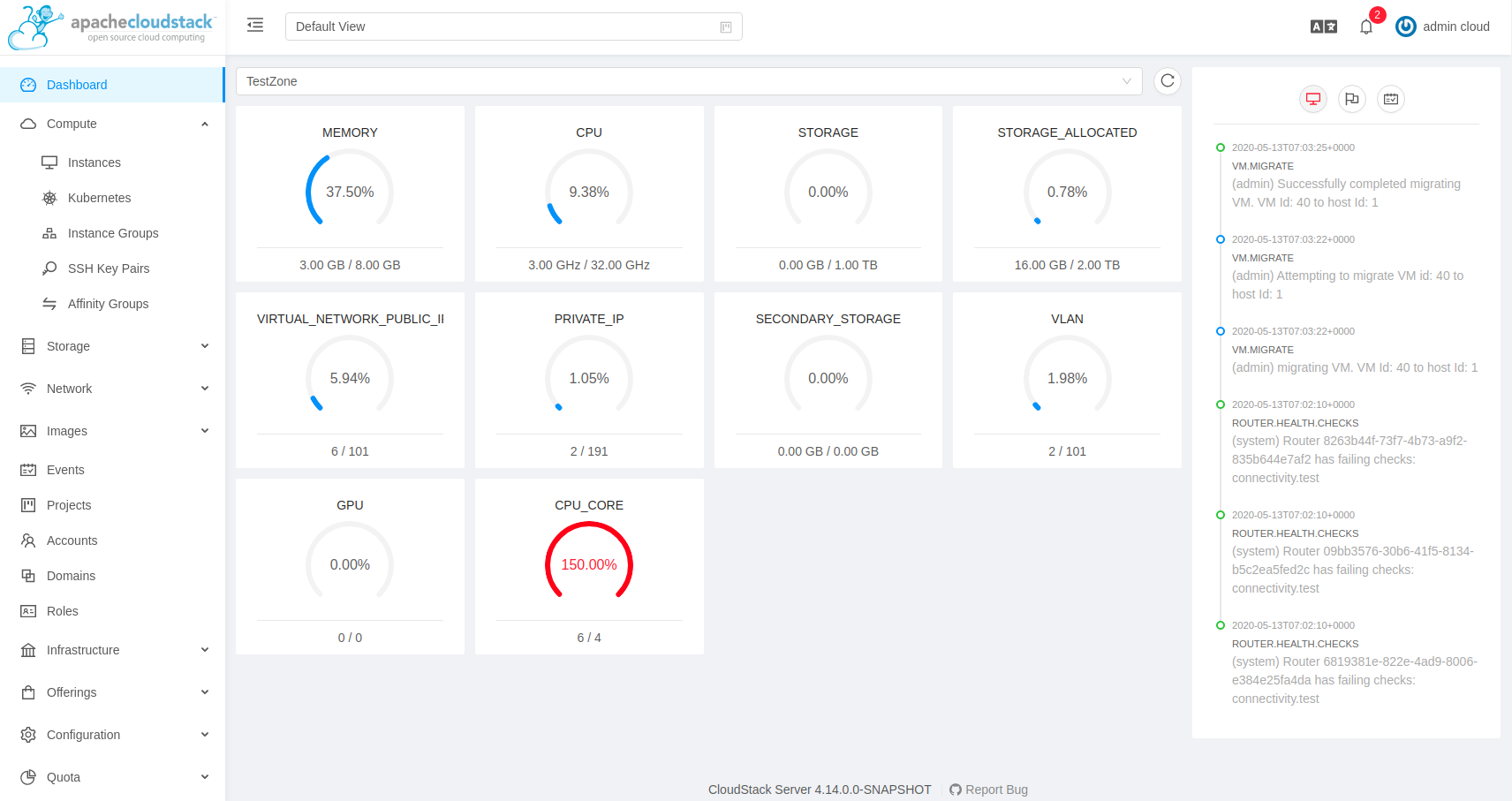
CloudStack UI
A modern role-based progressive CloudStack UI based on VueJS and Ant Design.
Getting Started
Install node: (Debian/Ubuntu)
curl -sL https://deb.nodesource.com/setup_12.x | sudo -E bash -
sudo apt-get install -y nodejs
# Or use distro provided: sudo apt-get install npm nodejs
Install node: (CentOS/Fedora/RHEL)
curl -sL https://rpm.nodesource.com/setup_12.x | sudo bash -
sudo yum install nodejs
Optionally, you may also install system-wide dev tools:
sudo npm install -g @vue/cli npm-check-updates
Development
Clone the repository:
git clone https://github.com/apache/cloudstack.git
cd cloudstack/ui
npm install
Override the default CS_URL to a running CloudStack management server:
cp .env.local.example .env.local
Change the `CS_URL` in the `.env.local` file
To configure https, you may use .env.local.https.example.
Build and run:
npm run serve
# Or run: npm start
Upgrade dependencies to the latest versions:
ncu -u
Run Tests:
npm run test
npm run lint
npm run test:unit
Fix issues and vulnerabilities:
npm audit
A basic development guide and explaination of the basic components can be found here
Production
Fetch dependencies and build:
npm install
npm run build
This creates a static webpack application in dist/, which can then be served
from any web server or CloudStack management server (jetty).
To use CloudStack management server (jetty), you may copy the built UI to the webapp directory on the management server host. For example:
npm install
npm run build
cd dist
mkdir -p /usr/share/cloudstack-management/webapp/
cp -vr . /usr/share/cloudstack-management/webapp/
# Access UI at {management-server}:8080/client in browser
If the webapp directory is changed, please change the webapp.dir in the
/etc/cloudstack/management/server.properties and restart the management server host.
To use a separate webserver, note that the API server is accessed through the path
/client, which needs be forwarded to an actual CloudStack instance.
For example, a simple way to serve UI with nginx can be implemented with the following nginx configuration (to be put into /etc/nginx/conf.d/default.conf or similar):
server {
listen 80;
server_name localhost;
location / {
# /src/ui/dist contains the built UI webpack
root /src/ui/dist;
index index.html;
}
location /client/ {
# http://127.0.0.1:800 should be replaced your CloudStack management
# server's actual URI
proxy_pass http://127.0.0.1:8000;
}
}
Docker
A production-ready Docker container can also be built with the provided Dockerfile and build script.
Make sure Docker is installed, then run:
bash docker.sh
Change the example configuration in nginx/default.conf according to your needs.
Run UI:
docker run -ti --rm -p 8080:80 -v $(pwd)/nginx:/etc/nginx/conf.d:ro cloudstack-ui:latest
Packaging
The following is tested to work on any Ubuntu 18.04/20.04 base installation or docker container:
# Install nodejs (lts)
curl -sL https://deb.nodesource.com/setup_12.x | sudo -E bash -
sudo apt-get install -y nodejs debhelper rpm
# Install build tools
npm install -g @vue/cli webpack eslint
# Clone this repository and run package.sh
cd <cloned-repository>/packaging
bash -x package.sh
Documentation
- VueJS Guide: https://vuejs.org/v2/guide/
- Vue Ant Design: https://www.antdv.com/docs/vue/introduce/
- UI Developer Docs
- JavaScript ES6 Reference: https://www.tutorialspoint.com/es6/
- Introduction to ES6: https://scrimba.com/g/gintrotoes6
Attributions
The UI uses the following:
History
The modern UI, originally called Primate, was created by Rohit Yadav over several weekends during late 2018 and early 2019. During ApacheCon CCCUS19, on 9th September 2019, Primate was introduced and demoed as part of the talk Modern UI for CloudStack (video). Primate was accepted by the Apache CloudStack project on 21 Oct 2019. The original repo was merged with the main apache/cloudstack repo on 20 Jan 2021.
License
Licensed to the Apache Software Foundation (ASF) under one or more contributor license agreements. See the NOTICE file distributed with this work for additional information regarding copyright ownership. The ASF licenses this file to you under the Apache License, Version 2.0 (the "License"); you may not use this file except in compliance with the License. You may obtain a copy of the License at
http://www.apache.org/licenses/LICENSE-2.0
Unless required by applicable law or agreed to in writing, software distributed under the License is distributed on an "AS IS" BASIS, WITHOUT WARRANTIES OR CONDITIONS OF ANY KIND, either express or implied. See the License for the specific language governing permissions and limitations under the License.